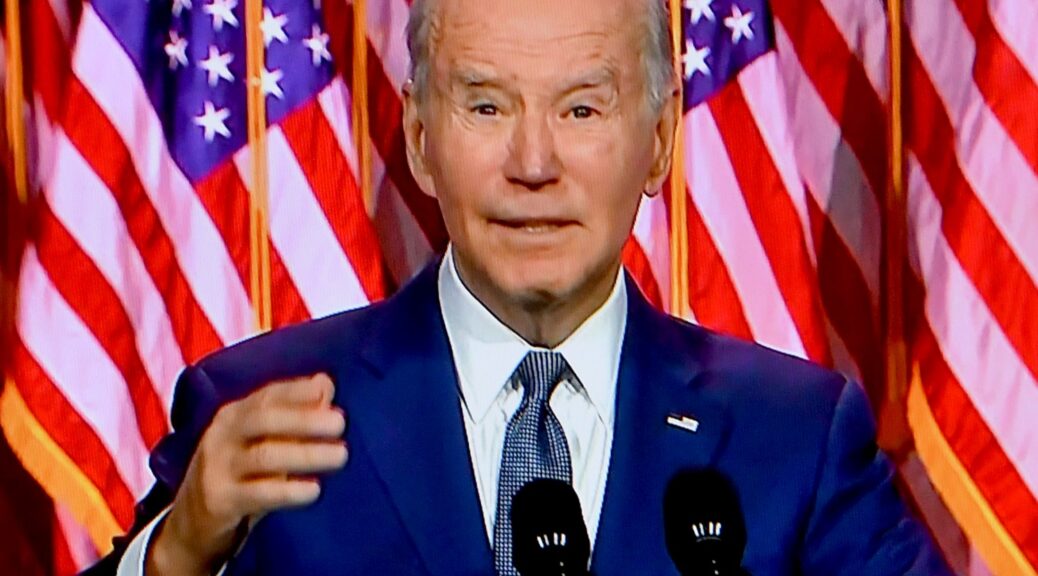
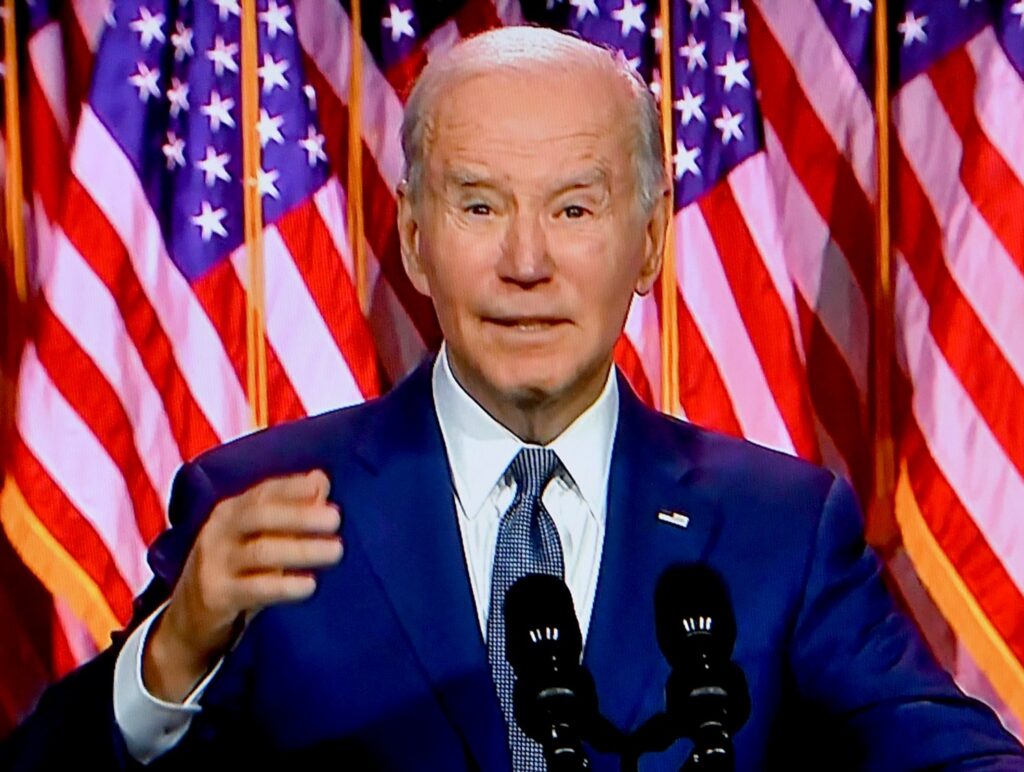
Trump’s initiation of unprovoked war on Iran at the same time his FBI chief Kash Patel has purged the FBI of counter-terrorism experts and anyone who was connected with the investigations into the January 6 insurrection, Trump’s attempted overturning of the 2020 election, the deportation of undocumented migrants (instead of the Iranian terror cells Trump has acknowledged exist), and focus on Trump’s campaign of retribution against political enemies has left the United States exposed.
In just a matter of days, there were at least three terror attacks – the bomb at NYC’s Gracie Mansion, the attack on a Michigan synagogue and another attack that killed at soldier and wounded two others at Old Dominium University in Virginia by a man who had already been convicted, imprisoned and released for his ISIS activity, instead of being monitored (the government was too busy deporting landscapers, healthworkers and construction workers).
When asked about the possibility of Iran, which has specialized in terrorism, unleashing attacks, Trump casually responded, “I guess,” adding “people die in war.” The Trump administration dismantled the Cyber Safety Review Board (CSRB), cut staff at CISA, and fired top NSA/Cyber Command leadership.
And this being Trump administration which only cares about politics and not public service, the administration blocked the release of a five-page statement, “A Public Safety Awareness Report: Elevated threat in the United States during US-Iran conflict,” which detailed “elevated threats by the government of Iran to US military and government personnel and facilities, Jewish and Israeli institutions and their perceived supporters, and Iranian dissidents and other anti-regime activists in the United States.” The report should have been distributed to states and localities.
So it is up to the states and localities to step up. New York State Governor Kathy Hochul has heightened its security and intelligence activities. –Karen Rubin, editor@news-photos-features.com
Governor Kathy Hochul announced nation-leading cybersecurity regulations and $2.5 million in grants to help communities affordably protect their drinking water and wastewater systems. This comprehensive, unified approach equips drinking water and wastewater operators with the framework and tools to bolster their cybersecurity posture against increasingly sophisticated and dangerous cyber threats while strengthening services that millions of New Yorkers rely on every day.
“Cyber attacks on our water infrastructure can disrupt services and threaten public health and safety,” Governor Hochul said. “My administration is protecting New Yorkers by modernizing regulations and providing resources to adopt these important safeguards. There is nothing more important than keeping New Yorkers safe.”
Water infrastructure is essential to public health, safety, economic stability and national security, making it an attractive target for cyber attacks. As systems increasingly rely on digital and internet-connected technologies, the need for cybersecurity safeguards continues to grow.
Delivering on the Governor’s State of the State commitment to strengthen the resilience and reliability of water and wastewater systems, the Departments of Environmental Conservation (DEC) and Health (DOH) developed minimum standards for wastewater and drinking water systems that are threat-informed, risk-centric, and cost-balanced. At the same time, the Environmental Facilities Corporation (EFC) created grants and no-cost technical assistance to support local implementation. Close coordination helped streamline oversight, eliminate duplication and align with federal cybersecurity guidance from the U.S. Environmental Protection Agency and the Cybersecurity and Infrastructure Security Agency.
The new threat-informed, risk-centric, and cost-balanced minimum standards developed by DEC and DOH include:
- Mandatory cybersecurity training for certified operators
- Cybersecurity incident reporting requirements
- Risk-based tiered standards to protect critical operations and sensitive information
- Designation of a cybersecurity lead role at larger drinking water systems
To support implementation, Governor Hochul is launching the new $2.5 million Strengthening Essential Cybersecurity for Utilities and Resiliency Enhancements (SECURE) grant program, administered by EFC. Applications open today. Funding includes:
- Up to $50,000 for cybersecurity assessments
- Up to $100,000 to implement cybersecurity upgrades
EFC’s Community Assistance Teams are available to provide no-cost guidance and tools to help water and wastewater systems implement cybersecurity best practices. Communities can request one-on-one consultations, apply for the SECURE grant, and access centralized training and best practice resources on EFC’s Cybersecurity Hub.
Guidance and additional implementation resources are available on DEC’s Wastewater Cybersecurity Resources and DOH’s Cybersecurity for Public Water Systems webpages.
New York State Director of Security and Intelligence Colin Ahern said, “In today’s threat environment, the security of our digital infrastructure is just as critical as the physical security of our reservoirs. Under Governor Hochul’s leadership, we are moving beyond reactive defense. By pairing nation-leading standards with the SECURE grant program, we are providing New York’s water sectors with the intelligence-driven framework and the muscle they need to preemptively harden our most vital systems against sophisticated global adversaries.”
New York State Acting Chief Cyber Officer Michaela Lee said, “Effective cybersecurity is not a one-time fix; it is a sustained partnership between the State and our local operators. Following the successful implementation of new standards for our financial and healthcare sectors, Governor Hochul is continuing her steady, sector-by-sector plan to fortify New York’s most critical infrastructure. By providing both the regulatory roadmap and the $2.5 million SECURE grant, we are ensuring that water and wastewater utilities have the guidance and resources they need to remain resilient in an increasingly digital world.”
“Governor Hochul’s nation-leading cybersecurity regulations reflect a steadfast commitment to protecting the health and safety of New Yorkers,” New York State Department of Health State Health Commissioner Dr. James McDonald said. “As drinking water infrastructure controls become increasingly digitized, safeguarding these systems is essential. These regulations strengthen our defenses, enhance monitoring and ensure public drinking water systems are prepared to respond quickly and effectively to potential incidents. We look forward to continuing our close collaboration with state and local partners to protect drinking water in New York State.”
New York State Environmental Facilities Corporation President and CEO Maureen A. Coleman said,“Thanks to Governor Hochul’s leadership, New York is pairing strong cybersecurity protections with meaningful support for local governments. EFC’s SECURE grant program and hands-on technical assistance will help communities implement these safeguards while keeping projects manageable and affordable.”
“Governor Hochul’s leadership is proactively enhancing cybersecurity across our water and wastewater systems to protect our environment and public health,” New York State Department of Environmental Conservation Commissioner Amanda Lefton said. “DEC is proud of the collaboration with State agency partners to help address cybersecurity threats and advance these critical water and wastewater infrastructure initiatives to safeguard communities.”
New York Conference of Mayors Executive Director Barbara Van Epps said,”Local governments operate the drinking water and wastewater systems that millions of New Yorkers rely on every day, and protecting those systems from cyber threats is a critical responsibility. Providing clear standards, financial support and technical assistance will help communities strengthen their defenses while maintaining the reliable services residents depend on. We thank Governor Hochul for prioritizing the security of this essential infrastructure.”
New York State Association of Counties Executive Director Stephen J. Acquario said,“Safe and reliable drinking water is essential to every community. As cyber threats grow more sophisticated, our water systems must be just as advanced in their defense. Additional cybersecurity grants give local water utilities the tools and technology they need to protect operations, ensure clean water delivery and keep our infrastructure secure. We thank Governor Hochul for her consistent leadership in water and wastewater safety and security.”
New York State Association of Towns Executive Director Christopher A. Koetzle said,”We congratulate Governor Hochul on her comprehensive approach to helping local governments across the state deal with the growing cybersecurity threats while also ensuring that our drinking water remains safe and available for all New Yorkers. This is an innovative and extensive approach to helping local governments protect their residents while also helping them maintain their critical frontline services.”
“Governor Hochul recognizes that cyber threat actors could target our public drinking and wastewater systems in an effort to inflict damage upon communities across our State, and, therefore, the highest level of security is necessary to protect our public utilities,” NYS Chief Information Officer and Director of the Office of Information Technology Services Dru Rai said. “These critical SECURE Act grant funding resources, along with new, nation-leading regulations, are exactly the steps we need to defend this vital infrastructure. At ITS, we are pleased to play an important role in implementing the Governor’s proactive, whole-of-government approach to cybersecurity. If it exists, we will protect it.”
New York State Police Superintendent Steven G. James said, “Law enforcement is constantly challenged to keep pace with the evolving online technologies exploited by criminals. As threats to cybersecurity and the health and safety of the public become more prominent, we are ramping up our efforts to protect the infrastructure of our drinking water and wastewater systems. Through the leadership and vision of Governor Hochul, we can cohesively safeguard an imperative element in New York State.”
New York State continues to increase its nation-leading investments in water infrastructure, providing $3.8 billion in financial assistance for local projects in State Fiscal Year 2025 alone, including $1.1 billion in grants. Governor Hochul set the national standard with a transformational $3.75 billion water infrastructure investment plan in the 2026 State of the State address, which would bring total State grants to more than $10 billion since 2017.
Improving the State’s Security
$38 million in state funding has been awarded to 17 counties and New York City to improve emergency communications for first responders, making New Yorkers safer. The Statewide Interoperable Communications Grant program supports local governments’ efforts to build and repair radio towers that allow them to communicate with other emergency responders during disasters and emergencies. Installing and maintaining these towers ensures that lines of communication continue to be clearly accessible in situations when they are needed the most.
Four New York public safety agencies involved with the security of the 2026 FIFA World Cup events received more than $17.2 million to protect against the threat of the illegal use of drones. The federal C-UAS Grant awards funding can be put toward the purchase of equipment and systems that help state and local agencies to detect, identify, track, monitor and/or mitigate unmanned aircraft systems that pose threats to public safety.